Outages At NYSE, United Airlines, WSJ.com Expose Digital Vulnerabilities

By Andrea Chang and Tracey Lien, Los Angeles Times (TNS)
The cyberoutages came one after another: one of the nation’s biggest airlines, its largest financial news publication and its main stock exchange.
Wednesday morning’s spate of technological foul-ups grounded United Airlines flights, sidelined the Wall Street Journal‘s website and halted trading for hours on the New York Stock Exchange. Their successive timing ignited widespread speculation about hacking attacks and conspiracy theories about who might be responsible.
Government and company officials said the causes were more mundane and technical, but the shutdowns nonetheless raise concerns about the vulnerability of vital organizations that can be easily crippled by malfunctions or cyberattacks.
As the world becomes more connected, such events expose serious risks for countries, companies and individuals who depend so heavily on fragile technology — often a mash-up of neglected old-fashioned processes and cutting-edge systems. Electricity grids, credit cards, social media, email, public transportation and GPS all have become indispensable to everyday modern life.
“These are incredibly complicated systems. There are lots and lots of failure modes that are not thoroughly understood,” said Jeff Schmidt, chief executive and founder of JAS Global Advisors, a security consulting firm. “Because the systems act so quickly, you have this really increased potential for cascading failures.”
On most days, the Internet and the myriad systems it powers can be counted on to work well enough. But security experts say problems are inevitable, whether due to hacking, human error, broken cables, buggy code or other unforeseen issues.
Technology will evolve and improve over time, but it will never be foolproof. What’s more important, experts say, is for organizations and individuals to better protect themselves against issues that are bound to crop up — an often neglected task.
Carl Wright, general manager of TrapX, a security-through-deception defense company, said much of the rapid deployment of new technology comes with little forethought about security.
“If we take a look historically at security budgets for most enterprises, most are about 10 percent of the whole IT spend of an organization. Sometimes, it’s as low as 6 percent,” he said. “Not a lot of the money an organization spends on tech to create capability for their business goes to securing it. What we need to see is a major shift.”
One problem: The best security systems can be costly. In other cases, the technology is still struggling to catch up to plug the holes.
But organizations can play defense. Business continuity plans and relationships with regulators and law enforcement can lead to faster response times when problems arise. Building in redundancies — using two Internet service providers, for instance — can serve as a backstop when one system crashes.
Training programs get employees up to speed on how to better handle failures. At the higher levels, nimble management teams can quickly identify an issue and respond to it — difficult in large corporations and heavily regulated businesses.
One strategy growing in popularity is for businesses to invite hackers to look for security vulnerabilities and reward them with so-called bug bounties.
Many organizations rely on third-party vendors to help them prepare for outages. A slew of security companies have cropped up, introducing new technology that replaces standard character-based passwords with images and even emojis.
Wednesday morning’s series of outages was an unusual occurrence, immediately prompting questions about a cyberattack.
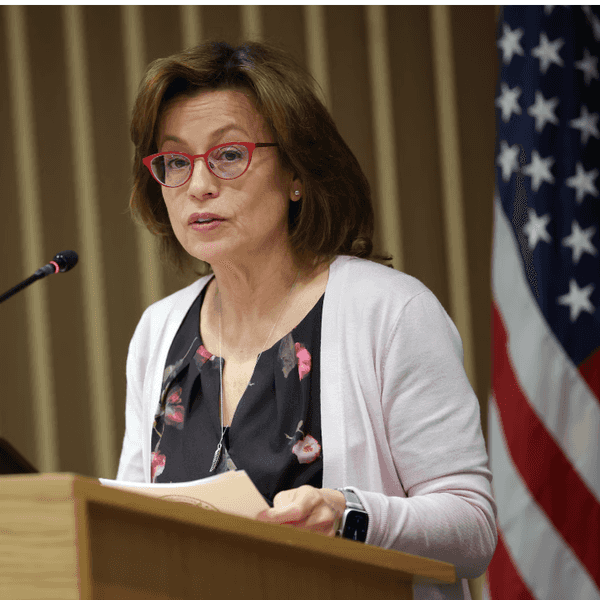
Homeland Security Secretary Jeh Johnson said in a statement that “the malfunctions at United and the NYSE were not the result of any nefarious actor. Both organizations cited technical issues for their downtime, which totaled 3 { hours for the NYSE and about 1 { hours for United.
A spokeswoman for the Wall Street Journal said its website’s outage was still being investigated.
Cybersecurity and the massive dependence on technology have also concerned lawmakers. On Wednesday, three of the nation’s top federal law enforcement officials strongly urged Congress and Silicon Valley to allow government authorities immediate, instant access to encrypted cellphones and other Internet devices.
The coincidental timing of that pitch — on the same day that the outages occurred — might bolster officials’ case that more stringent measures are needed to protect American computers and national infrastructure from cyberattacks, despite objections from Silicon Valley.
On Tuesday, the nation’s top cryptographers criticized Washington demands for companies to alter their technology and allow law enforcement to secretly see and read what is being sent and received on cellphones and computers.
“Lawmakers,” the scientists warned, “should not risk the real economic, geopolitical and strategic benefits of an open and secure Internet for law enforcement gains that are at best minor and tactical.”
(Times staff writer Christine Mai-Duc contributed to this report.)
(c)2015 Los Angeles Times. Distributed by Tribune Content Agency, LLC.
Photo: A United Airlines employee, center on phone, works with passengers at the economy check-in area of O’Hare International Airport as flights were delayed due to a stoppage on Wednesday, July 8, 2015. United grounded all U.S. flights because of “automation issues.” Planes at O’Hare were not leaving the gates, and some passengers said they were unable to book flights. (Jose M. Osorio/Chicago Tribune/TNS)