by Megha Rajagopalan, ProPublica
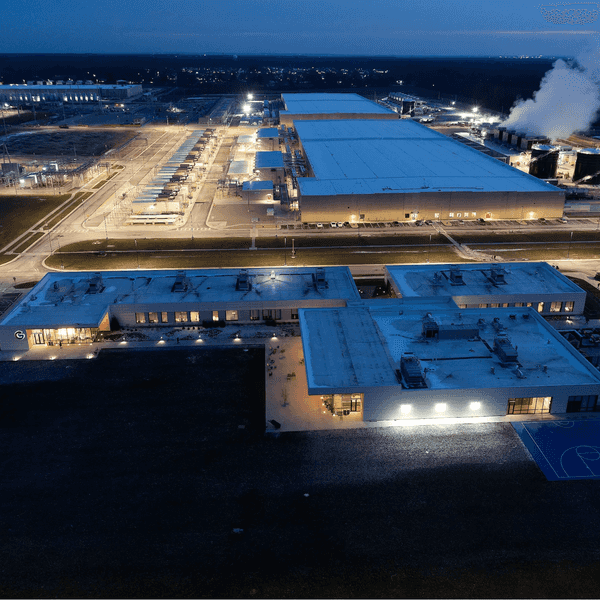
Last week, the Department of Homeland Security revealed a rash of cyber attacks on natural gas pipeline companies. Just as with previous cyber attacks on infrastructure, there was no known physical damage. But security experts worry it may only be a matter of time.
Efforts to protect pipelines and other critical systems have been halting despite broad agreement that they’re vulnerable to viruses like Stuxnet — the mysterious worm that caused havoc to Iran’s nuclear program two years ago.
The Frankenstein-like virus infected a type of industrial controller that is ubiquitous — used around the world on everything from pipelines to the electric grid.
Experts say manufacturers haven’t fixed security flaws in these essential but obscure devices.
Why hasn’t more been done? Here’s why Stuxnet remains a top national security risk.
Q. What is Stuxnet, anyway?
Stuxnet first made headlines when it burrowed into computers that controlled uranium centrifuges in Iran’s renegade nuclear program. Its self-replicating computer code is usually transmitted on flash drives anyone can stick into a computer. Once activated, the virus made Iran’s centrifuges spin out of control while making technicians think everything was working normally — think of a scene in a bank heist movie where the robbers loop old security camera footage while they sneak into the vault.
Q. Who created it?
Whoever knows the answer to this isn’t telling — but if cybersecurity researchers, the Iranian government and vocal Internet users are to be believed, the two prime suspects are the U.S. and Israeli governments.
Q. How does it work?
Stuxnet seeks out little gray computers called programmable logic controllers, or PLCs. The size and shape of a carton of cigarettes, PLCs are used in industrial settings from pretzel factories to nuclear power plants. Unfortunately, security researchers say the password requirements for the devices are often weak, creating openings that Stuxnet (or other viruses) can exploit. Siemens made the PLCs that ran Iran’s centrifuges; other makers include Modicon and Allen Bradley. Once introduced via computers running Microsoft Windows, Stuxnet looks for a PLC it can control.
Q. How big is the problem?
Millions of PLCs are in use all over the world, and Siemens is one of the top five vendors.
Q. After Iran, did Siemens fix its devices?
Siemens released a software tool for users to detect and remove the Stuxnet virus, and encourages its customers to install fixes Microsoft put out for its Windows system soon after the Iran attack became public (most PLCs are programmed from computers running Windows.) It is also planning to release a new piece of hardware for its PLCs, called a communications processor, to make them more secure — though it’s unclear whether the new processor will fix the specific problems Stuxnet exploited. Meanwhile, the firm acknowledges its PLCs remain vulnerable — in a statement to ProPublica, Siemens said it was impossible to guard against every possible attack.
Q. Is Siemens alone?
Logic controllers made by other companies also have flaws, as researchers from NSS labs, a security research firm, have pointed out. Researchers at a consulting firm called Digital Bond drew more attention to the problem earlier this year when they released code targeting commonly used PLCs using some of Stuxnet’s techniques. A key vulnerability is password strength — PLCs connected to corporate networks or the Internet are frequently left wide open, Digital Bond CEO Dale Peterson says.
Q. What makes these systems so tough to protect?
Like any computer product, industrial control systems have bugs that programmers can’t foresee. Government officials and security researchers say critical systems should never be connected to the Internet — though they frequently are. But having Internet access is convenient and saves money for companies that operate water, power, transit and other systems.
Q. Is cost an issue?
System manufacturers are reluctant to patch older versions of their products, government and private sector researchers said. Utility companies and other operators don’t want to shell out money to replace systems that seem to be working fine. Dan Auerbach of the Electronic Frontier Foundation, formerly a security engineer at Google, says the pressure on tech companies to quickly release products sometimes trumps security. “There’s an incentive problem,” he said.
Q. What’s the government doing?
The Department of Energy and the Department of Homeland Security’s Computer Emergency Readiness Team, or CERT, work with infrastructure owners, operators and vendors to prevent and respond to cyber threats. Researchers at government-funded labs also assess threats and recommend fixes. But government agencies cannot — and do not attempt to — compel systems vendors to fix bugs.
The only national cybersecurity regulation is a set of eight standards approved by the Federal Energy Regulatory Commission — but these only apply to producers of high-voltage electricity. A Department of Energy audit last year concluded the standards were weak and not well implemented.
Q. So is Congress weighing in?
Cybersecurity has been a much-debated issue. Leading bills, including the Cyber Intelligence Sharing and Protection Act, would enable government and the private sector to share more threat information. But while CISPA and other bills give the Department of Homeland Security and other agencies more power to monitor problems, they all take voluntary approaches.
“Some of my colleagues have said nothing will change until something really bad happens,” said Peterson, whose consulting firm exposed vulnerabilities. “I’m hoping that’s not true.”
Q. What does the Obama administration want?
The White House has called for legislation that encourages private companies to notify government agencies after they’ve faced cyber intrusions, and recommends private companies secure their own systems against hackers. But the White House stops short of calling for mandatory cybersecurity standards for the private sector.